In 2014, the United States Secret Service was wiretapped through a Google Maps exploit by an individual who wanted to prove how easy it was to game the system. This person risked a life in prison to expose this cybercrime – and today, he joins us in this episode of Coding Over Cocktails to tell you all about it.
Listen in as we explore the world of hacking through the eyes of a world-renowned cybersecurity expert, ethical hacker, and former US marine. We talk to him about his experiences and views on hacking and cybersecurity; how attacks are becoming more and more sophisticated; and how organizations can potentially address and protect themselves from these cyberattacks.
Episode outline
- Bryan Seely answers: how does one go from being a Marine to a hacker?
- What was it like wiretapping the US Secret Service?
- Do companies value market gain over fixing their business processes?
- “There are people who don't want to look at anything that they would consider a weakness.”
- How do ethical hackers choose their target?
- How can organizations stop these attacks from happening to them?
Transcript
Kevin Montalbo
Welcome to episode 41 of the Coding Over Cocktails podcast. My name is Kevin Montalbo. Joining us from Sydney, Australia is Toro Cloud CEO and Founder, David Brown. Hi, David!
David Brown
Good morning, Kevin!
Kevin Montalbo
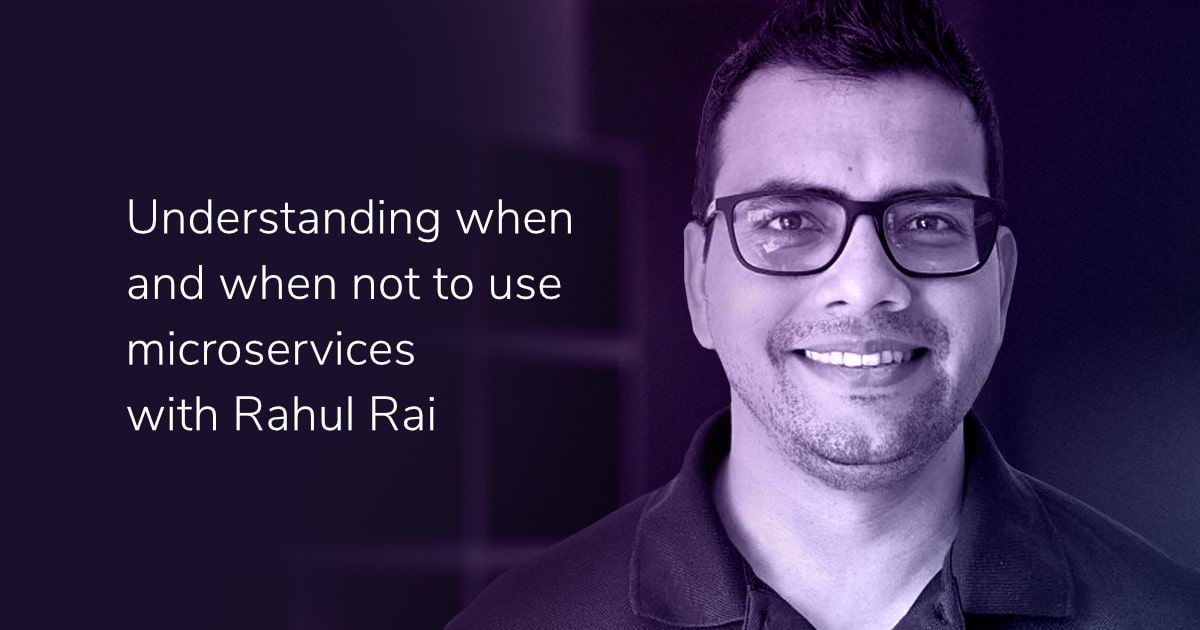
All right. And our guest for today is a world-renowned cybersecurity expert, ethical hacker, author, and former Marine. He was named one of the most famous hackers in 2014 when he became the only person to ever wiretap the United States Secret Service and FBI. He is now a professional keynote speaker and podcast host, invited to hundreds of conferences and events worldwide, has written a book called Cyber Fraud: The Web of Lies, and now works as a Senior Security Architect for Cyemptive Technologies.
Ladies and gentlemen, joining us for a round of cocktails is Bryan Seely. Hi, Bryan! Welcome to the show!
Bryan Seely
Howdy!
Kevin Montalbo
All right. So, we want to jump right into the questions, but first we want to ask you, how does one go from being a Marine to an ethical hacker?
Bryan Seely
Well, have you ever made a bad decision in your life?
David Brown
Which one was the bad one?
Bryan Seely
Well, the Marine aspect was kind of crucial to it. It gave me a lot of confidence in being able to move forward. But when the ethical hacking thing came up, I had been going through a divorce. I was bored. I didn’t have a lot of time. I actually got clean and sober for the first time after coming back from my rack to deal with things properly. So, getting clean and sober left me with a lot of free time. I wasn't going to bars and I love doing podcasts. And I don't mind when I have friends who drink. I keep wine in my home, but today is my four year anniversary of being sober, which I find super funny that you can be on Coding Over Cocktails. It’s hilarious.
David Brown
Well, congratulations and sorry about that.
Bryan Seely
No, not at all. Like, do you like broccoli?
David Brown
Broccoli, yes.
Bryan Seely
I do not. Does that mean I would demand that you stop eating broccoli? I mean, if you're going to steam it, don't do it in the office microwave maybe. But other than that, it wouldn't preclude you from having to. Go, eat broccoli! Do whatever. Is it ruining your life? Do you have a broccoli addiction? If you don't, you're fine. It doesn't affect me whatsoever.
David Brown
Well, that's good. Now that we've got that sorted out, maybe we can talk about your ethical hacking. So look, when I hear “hacker”, I get these images of a computer nerd in a darkened room. Actually, not that dissimilar to what you're sitting in now with glowing lights around you.
Bryan Seely
I resent the accuracy of that.
David Brown
Wearing a hoodie, feverishly entering lines of code, breaking through firewalls, accessing confidential information. But in reality it's just as likely a hacker could be someone that is looking for exploits in a business process or a system design, right?
Bryan Seely
Right.
David Brown
Is that how you got into this?
Bryan Seely
It was a by-design system, exploiting a system that had multiple moving pieces.
The time with Google Maps and wiretapping the Secret Service was not a software vulnerability or breaking into a firewall or NCIS-type thing. It was a by-design system, exploiting a system that had multiple moving pieces. So, if you built a location on Google Maps for your business, you would get a postcard, or if it already existed and you needed to claim it, you would then be able to get a phone call. So, that phone call would be a way to verify the accuracy of that information, that you control that phone number, all it means. But that phone number then becomes the trust anchor for all of your data related to it. That's the one thing you can't change. Everything else you can change at that point. So, what I did was built something in a place that I had control over the phone number and then changed all the data associated with it, and then re-triggered a verification, because you could disassociate with the listing.
Say, I don't own this business anymore. It's not mine. I don't want it. Reverify the phone number. But now the address, you can move all the way across the country. These systems were all by design. They all existed in the way that they designed their products at Google Maps. But it was easy to exploit and then become a really large problem. On a global scale, to give you the idea of business categories like locksmiths, that type of thing, if you look up on Bing Maps, in which Bing is a much worse option than Google Maps, Google is hands down the best at this, at getting rid of spam. Bing Maps has more locksmiths in Redmond, Washington state than there are actual locksmiths in Washington state.
David Brown
Because they are spamming the system. They're spamming it, right?
Bryan Seely
Right, and by names like “AAA Locksmiths”, “24/7-Ready Locksmiths”, “Locksmiths All Day Long”, like every name combination you could possibly come up with, putting up fake reviews on each one of those, boosting them to the top ranking spots for those keywords. And when they get flagged, it doesn't matter to them because they've got multiple backups. The same thing is happening on Amazon, where people have found ways to review products. So, you can launch a product and get it to the top of Amazon,you're a millionaire. So many people are going to see it if you can pop into that recommended spot. “Other people have bought this.”
I have seen Amazon accounts that have been hijacked only for the purpose of buying something, sending it to someone, but they didn't use a pre-stored credit card. So if they broke into my account, for example, they'd use their own card, then shipped the item to a different address. And why would they do that? They want verified buyer reviews. It's worth the effort because really, if you look at it and you're like, “Did you break in and clean my house?” No crime occurred according to the person whose account was accessed other than their name was used as a review.
David Brown
Yeah, and like you mentioned that in, I think it was Redmond? You're saying that there's more locksmiths advertised on Google Maps and they're actually locksmiths.
Bryan Seely
But not on Google. Google Maps.
David Brown
You were saying in one of your talks, there would be ads like, you know, “We will do a call-out service and fix your locks by $15,” or something like that.
Bryan Seely
Right. So $15 lockout specials.
David Brown
Yeah. So, it brings us back to the question, “Why would there be more locksmiths advertised than there actually are right there?” So, what are they trying to achieve? What's the end goal here?
Bryan Seely
Redundancy. And 90% of people will click the top one or the second to the top one, or some people will pick the one closest to them or the one name that they think they heard of, or they resonate with. So, there's 90% for the first one, 5% for the second one, another 5% for the third or fourth. And then a 0.1% for all of the remaining listings because they get calls. We just don't know exactly why, but they're not the top spot, but if the top spot and all 10 subsequent ones are the same person, it doesn't matter because if one of them gets flagged as being spam, it's like a pipeline for leads in a CRM. Like, you just want to have a ton going in. Because you know, a ton are going to lose. You're going to have attrition.
David Brown
So it's a numbers game. Your TED Talk on wiretapping the United States Secret Service using Google Maps has received over 4 million views. And obviously you've already alluded to this, some of the techniques in which you achieve that, but for some of our listeners, which perhaps haven't listened to the TED Talk, could you briefly run us through the process of what occurred again?
Bryan Seely
I found some fraud that we just talked about here. Business listings, all over the world. I had worked for a company a few years prior that was doing this kind of thing. When I got into the data entry period of it, I didn't know that they were fake companies. It was just orders. “Hey, input this data. Hire a team in the Philippines. Hire a team in Bangladesh. Hire a team wherever. Input data. Go and generate stuff.” At one point, the company paid a screenwriter to write, I think it was like a hundred thousand reviews? Like an out of work screenwriter during the writer's strike, he wrote a hundred thousand autoblast reviews. All of them, unique.
David Brown
This is for a company you worked for, did you say?
Bryan Seely
Yeah.
David Brown
Right, so this is how you start to become aware of this exploit.
Bryan Seely
Oh yeah. And figuring out how to get around stuff. And then there's other communities of people like Warrior Forum, BlackHat Forum, and all sorts of other places where people have either products for how to do this kind of thing. And there's legitimate courses out there that people try to help you figure out a way to generate leads, almost like a whitewashed term for lying. “Go lie. Just lie. It's good. You can just say you're another business. It's okay. It's just getting leads.”
But we call that lying and it's fraud. The basic definition being “lying to get money from someone when they wouldn't have given it to you if you had told the truth.” Like, are you going to trust a plumber from Florida? If you live in California? No. Why would you call them? That wouldn't make any sense. And most of the time, that's why these people are shady about it.
David Brown
So that's, and as I understand it, your technique to prove this concept in a rather old way, let's say, was you verify the number, for some reason you chose the Secret Service because I'm guessing that was going to be a fairly high profile target to prove your point. You hijack the number and then presumably you just used a number which the service can buy and then you can transfer the call?
Bryan Seely
What happened then was, there were business listings for ATMs, which don't have a phone number most of the time. And don't have anyone claim it, because who gives a s*** about owning an ATM? You don't need it on the map. So, you could add a phone number using Google Map Maker, which was a product that I helped make go away because it was a part of the process. So, adding information as sort of a correction or an edit. So you can add a phone number to an ATM, go back a couple of days later, claim it as your business it now verifies because you have the phone number, whether it's RingCentral or VoIP or some sort of number. And then you could move that ATM anywhere in the country and change the addresses a million times as you want because the thing that couldn't be changed was the phone number.
But if you verified with the postcard to verify your address, that's the thing you couldn't change. So, it was one or the other and they've changed some of that process now. I'm pretty sure people still do it using postal service mail forwarding. So, for example, you could go and send a verification postcard for “Brian Seely Consulting Service, 1 World Trade Center, New York, New York.” Whatever the zip code is. And then go set up a postal service mail forward for that business name saying, “I'm going on holiday. I need all my mail forwarded.” You don't have to register with the postal service when you get a business. You only have to tell them when you need mail to be shifted. They’re just by default, going to try to deliver the mail. So, the mail postal service pretty much everywhere operates on a whitelist-until-blacklist or change needed.
So everything is allowed until you say, “Specifically do this thing.” So, if no one has a mail forward, they're just sending everything everywhere and then everything stays there. If the transfer needs to happen, then you have to make an edit. It would go to chaos if everyone had to register where they lived and people would pitch a fit to have to register where they lived. It would be like, “Show me your papers.” That's the level of like, government intervention and people get really nervous here about that kind of thing.
David Brown
Well, I lived in Hong Kong for six and a half years. And you would regularly have to show proof of address.
Bryan Seely
I grew up in Tokyo and you have to have your Alien Registration Card on you at all times. You have to show a utility bill. Like, you have to pay for the television service. Even if you don't own a TV. And like there's all sorts of, you can't not have your address be correct on your license or that kind of thing. But it's just policy and everyone follows it and it's no problem. Yeah.
David Brown
So the difference between a black-hat hacker and a white-hat hacker is, as I understand the career, it's whether you get paid or not.
Bryan Seely
Black-hats try to get paid. It's just about you. If every job you do is liable for criminal prosecution, you're not as good. It's like being a company nowadays. You have to be a hundred percent perfect and never make a mistake. Or you're going to get ransomware at some point. If you are the best criminal ever, the idea is you do a couple big things and then you stop crime. Because if you're going to get caught eventually, you're not going to beat everyone else that's trying to catch you. And your personal freedom is important. Like, I don't want to be in an orange jumpsuit in a cage somewhere. It washes my skin. I look terrible in orange. I get that.
David Brown
So, white hat hackers, conversely, they'll do it for the benefit of society. So, in this case, as I understand it, before you went to the Secret Service, you went to Google and said, “Look guys…”
Bryan Seely
Yeah, I had been going back and forth with them for weeks. Yeah. I reported it through the proper channels. They said it was spam. This was not a problem. I made some funny business listings to try to get them to think, “Okay, maybe this is what he says it is,” but they were flat out telling me, “You're a liar. You can't do what you just said you did.” So on the news -- I had a news crew with me -- they recorded me changing the Library of Congress in Washington, DC, to the “Zoolander School of Kids Who Can't Read Good.” And we filmed it. And then the news agency called the Google people and there they said on the phone “What are you saying? It’s impossible.” And they said, “Well, we just filmed him doing it,” and they hung up. It was like, “We’re not calling you an a******. We're just telling you, we did this. You said it's not possible.”
David Brown
Now the really interesting part in your TED Talk, I found about -- this is obviously when the Secret Service rang them -- it got their attention and they shut down the service for a few months. But what I found really interesting was that they reintroduced it after the news story had died down a bit without actually implementing any changes.
Bryan Seely
Yeah that was fun. Wasn't it? So I'm online again. And then nothing happens.
David Brown
So presumably the issues have been improved since then. And like you said, it might be that some search engines are better or worse than others, but do you find that there's a genuine issue that businesses don't really want to address these failures in their process and are perhaps focused on commercial gain or something? Or market share as opposed to fixing these exploits?
Bryan Seely
There are people who don't want to look at anything that they would consider a weakness.
I think you just raised a really good fundamental question about what human life is about. A lot of people I served with get divided into two categories. There's the people who are, “I'm great. I didn't do anything wrong. America is awesome. We're the best country in the world. We make no mistakes. Everything we do is amazing.” And then there's the ones of us. We're like, “Well, where's the data to support that. Because we're not the best at literacy. We've got the most guns, if that's the metric you're using to measure great.” But there are people who don't want to look at anything that they would consider a weakness. And then there's the people who want to look at the weaknesses to address them, to fix them.
Like alcoholics, for example. The first step is admitting you have a problem. And if you don't, then you're just, “Oh, well it couldn't be the drinking. All these DUIs, it's those cops. They've got it out for me.” You have to address the weaknesses in your company. It makes sense. It's a mature response. It's an adult way of looking at things for shareholders, for maximizing value, for bringing up the value of a company is to quickly find out how people would break into your home or your company and fix those things first. Just knock them out one at a time without emotion, “Hey, we're going to fix this broken door,” “Hey, we should put a lock on this.” That kind of thing.
David Brown
Yeah. But it's interesting, isn't it? Because when you bring it to their attention, there's a significant exploit like you did, then sure, you would expect them to fix it. I guess there's a lot of business processes. Because in effect, this was an exploit of a business process.
Bryan Seely
Does it make it less devastating?
David Brown
No, not at all, but companies have thousands and thousands of business processes. So, I'm wondering what you would recommend. How do they go about fixing issues, which they're not aware of? Like how do you go about choosing your targets? Because you know, you've obviously found other exploits on other systems besides Google Maps and that you've got a number of talks on those. So, how do you go about finding it? Because I'm thinking it might help companies find ones within their own organization.
Bryan Seely
Take the ego down a notch. Everyone has made mistakes.
I recommend companies engage organizations like Bugcrowd or HackerOne, any bug bounty program, at least from the coding and technical attributes. Because the people that end up working for you on one, chances are they'll probably work on helping you find multiple issues that you didn't know were possible. It's like, you don't need to go and hire the best programmer and then have him on salary for the rest of his life. You can get access to those people through these types of platforms who are then going to find out where your mistakes are. It's like hiring a grammar Nazi to proofread your document. Like, he's gonna give you the straight answer because he's getting paid, there's incentive and you're not looking at it from an immature standpoint of, “How dare you criticize my work.” Be like, “Hey, are you human? Hey, guess what? If you haven't made a mistake yet, then you might be Jesus. If you have, you're probably not. If you're Jesus, we're going to have to have a whole bunch of other questions.”
So like, take the ego down a notch. Everyone has made mistakes. Michael Jordan has missed more shots than most of us have ever taken. I mean the failure rates are kind of up there, but he's the greatest. You have to look at those little shortcomings. The people who end up working on those technical vulnerabilities will then start to see the business process vulnerabilities as well because it's like looking at the website and what it's doing for a user and how they're going to click on stuff while simultaneously looking at the code behind it, looking for any clue.
Because sometimes, the way the bug bounty or the chasing of these technical vulnerabilities is like, your head’s above water. You're a normal user. And then you go down under the surface first, it's up and down and you're not sitting, looking at matrix code all day long. Sometimes, you're just clicking on the same form over and over and over again, watching how it works and what it connects to. And then noticing that there's no “s”, “Oh, you forgot this.” Something simple. The typo, you didn't use a secure port or there's no TLS between these two elements or there's this, that, or the other. It's people fact checking and just double-checking, triple checking your work because it's important. Because that one mistake ends your company. Is your ego going “Oh, we did everything great,” worth not being a company? I mean, that's what it boils down to.
David Brown
This experience you've had, finding exploits in systems has led to a career in the space. And you've recently joined Cyemptive and they have a patented technology that monitors the state of files rather than state of APIs to eliminate cyber threats before a problem is initiated. So that sounds interesting to me. Tell me about that. Tell me about your work there and what you're doing, what the company is trying to achieve.
Bryan Seely
I've been with Cyemptive for a little over a year and a half. It's one of the first companies I've been really excited about. I worked for a vendor company, they were one of our vendors and I got a chance to sit with the CSO, COO and the CEO, all in a meeting with my boss at the time. And it was like a eureka moment. They figured something out actually works. Most antivirus products monitor 2% of the APIs within an operating system at any given point. Trying to maximize utility without completely just swamping the processor. Because we've all heard the jokes about, whether it's like old Norton or Symantec or whatever it is being the biggest virus that you have on your computer because of how much processor it consumes. So, no antivirus product monitors for every possible action that a computer. There's too many things going on.
You'd need multiple other processors just to run all that stuff. And it would be cost prohibitive. So, we have products that protect from ransomware, Sleeper ransomware, as well as stuff that's not been seen. So, it's not heuristics-based file scanning. The analogy I like to use when I'm explaining it to my kids is, I got a box from Amazon. And it's red and I opened the red box and it's six inches by six inches by six inches. And it's this tiny, little box and uh-oh, it's all spiders. The next day, are you going to open the red box that’s exactly the same look as the one that had spiders in it? No, you are not.
But if it's blue, not red, “Hey, it sounds like spiders. Still it’s blue. Go ahead and get the scissors. This one's good.” “Hey, that iceberg looks fine, Titanic Crew.” I'm sure we've never died from an iceberg before. Is it problematic? We'll see.
That’s not a great way as ransomware gets worse, as problems and malware gets worse because it's not just, “We're robbing you in the present. We're robbing you in the future too.” Like, “We're going to go steal your intellectual property. We're going to hold all of your private information for ransom. Then we're going to try to extort you or we're posting it on the web for everyone to see,” like EA and the source code with them. Or Accenture got hit today with LockBit too. The LockBit ransomware group is now recruiting insiders. It's like, “Hey, is your boss a d***? How would you like to make some money? Just download this and we'll take care of the rest.” I know some people who would. Unfortunately, those are the people who wouldn't tell you. They got bit by the zombie. We know some of those people they're like, “No, it's fine. It was a scratch. We're good. We're good.” But that guy is going to eat all of you in a few minutes. So, they're getting more sophisticated. The damage is being maximized. How are we going to stop it?
David Brown
Well, that's going to be my next question.
Bryan Seely
At Cyemptive, I've seen some of the ways. Do they have patents? Intellectual property? My direct boss was 35 years at the NSA. And if he boards a plane, I'll trust that airline. If he won't eat at a restaurant, I won't eat at that restaurant. I mean, I'm pretty sure he doesn't go to Taco Bell in his sixties. But the idea being, if he's saying, “Okay, these guys are good. These guys are bad.” He's got access, or has had access to all of the secrets. Like, I don't even want to know, because that's just too much information for one person, but he's got the best sense of humor.
And I know nothing about him. Like nothing. I think his name is Gary. But he's one of the smartest people I've ever met. And he's brilliant. These people have dedicated actual solutions that detect people within seconds hacking into your network.
David Brown
Since you've got involved in that space and you talk about ransomware, is that something you're coming up against in terms of clients and businesses, which are experiencing this and the ways that they're responding to it?
Bryan Seely
Between Cyemptive and then my private consulting or personal career of public speaking, almost every single thing is related to ransomware in some way, shape or form. What are the current coming threats? Is there something better than ransomware or worse? Super ransomware. It's like, “Oh, this ransomware has got AIDS. And now you're going to get sick in the real world.” “We've mixed COVID and ransomware together. Your computer can now make you sick.” Like what's next? What's coming?
And that usually is the basics to stop these kinds of things, backups. From what I understood, Accenture put out a statement saying they were able to restore from backups to prevent loss or downtime or whatever. They didn't have to go and pay the ransom. They're not gonna be able to stop the extortion attempt.
Number one, if anyone releases all the private documents of Accenture, snooze fest. PowerPoint presentations, case studies, we've got metrics. Holy crap. That's a big data dump I do not want to pile. Like, who wants to do that? That's a job. Here's a job. I just gave you a boring job. Like, read through all this stuff and learn about another company. Like, oh my God.
I mean, I might want to find some PowerPoint presentation templates that say, “Ooh, that one's really pretty. I like that.” But other than that, like, I feel bad for them. I'm glad that they set a good example because they represent the top tier of consulting, right? I used to work for a company called the Avanade that was an Accenture-Microsoft partnership. It's nice to see that they're still maintaining a high level of expertise. So, backups, training your people, it's not the sexy stuff. It's, “Learn how to dribble so you can play basketball.” It's the fundamentals. But so many people just don't do it. It's embarrassing.
David Brown
You mentioned that they're starting to try and recruit within the organization. I know a lot of the exports come from people inadvertently clicking on an email and exposing their passwords and stuff like that. Getting back to our access to an organization. Do you find that the threat from ransomware is coming off shore, or is it also a domestic issue where people are trying to attack?
Bryan Seely
It's impossible to get any good real metrics. I mean, most of it is originating from organized groups in Eastern bloc, Cyrillic languages, should I narrow it down? It rhymes with “Shmussia”. Technically not them, but people nearby or they know of who it is or they're related, but it doesn't mean to say that they're all bad. It's just, they're the most sophisticated adversaries in the United States hacks. And if Israel suddenly became a problem, we'd have a whole big issue with them too, because they're probably within the top three capable offensive hacking groups on the planet. Is Israeli Russian or Russian bloc or old USSR Soviet Union? And then China, with North Korea following them, but they're not sophisticated. And was anyone expecting them to be?
David Brown
It's an interesting topic, Brian. How can our listeners follow you and get more information about this from you?
Bryan Seely
You can find me on Twitter or LinkedIn or Bryanseeley.com, or you can start knocking on houses and eventually you'll find me.
David Brown
And I believe your handle is “bryanthemapsguy”?
Bryan Seely
“Bryanthemapsguy” on Twitter and I think LinkedIn or Bryan Seeley on Facebook. I'm on Telegram, you know, most places.
David Brown
Bryan, very interesting to talk to you today. Thanks for joining our program.
Show notes:
- Cyemptive Technologies
- Accenture LockBit Ransomware Attack
- Bryan Seely on Twitter